Software update problems are a common headache for users, ranging from frustrating delays to complete system crashes. This comprehensive guide explores the various types of update issues, from installation failures to compatibility problems, and provides actionable troubleshooting steps.
Understanding the intricacies of software updates, including system requirements, error messages, and vendor support, is crucial for a smooth upgrade process. This guide offers practical advice to prevent and resolve problems effectively.
Identifying the Problem
Software updates, while crucial for maintaining system stability and security, can sometimes encounter unexpected issues. Understanding these problems is essential for effective troubleshooting and resolution. This section details various types of update problems, their causes, and how user actions can contribute to these issues.
Types of Software Update Problems
Software update problems encompass a range of issues, from minor inconveniences to significant system failures. These problems often manifest in error messages, application crashes, or unexpected system behavior. A thorough understanding of these diverse problem types is vital for effective troubleshooting.
Common Error Messages and Their Causes
Various error messages accompany software update problems. For instance, “Insufficient disk space” indicates a lack of storage for the update files. “Update failed due to corrupted download” suggests the update file was damaged during transfer. “Update conflict with existing software” signifies incompatibility between the new update and existing applications or drivers. “Error 1234” might refer to a specific issue related to the update process, needing more detailed investigation.
User Actions Triggering Update Problems
User actions can inadvertently trigger software update issues. For example, interrupting an update mid-process, disconnecting from the internet, or having insufficient system resources can all lead to problems. Carefully following update instructions and ensuring stable internet connectivity and sufficient system resources are critical to prevent these problems.
Compatibility Issues vs. Update Conflicts
Compatibility issues and update conflicts are often confused, yet they are distinct problems. Compatibility issues arise when a software update is not compatible with the user’s existing hardware or software configuration. Update conflicts, on the other hand, occur when a new update is incompatible with existing software components or files, leading to conflicts in functionality or operation. Understanding this difference helps users identify the root cause and apply the appropriate troubleshooting steps.
Software Update Failure Modes
The following table Artikels various failure modes during software updates, including their descriptions, severity levels, and typical causes:
| Failure Mode | Description | Severity | Typical Cause |
|---|---|---|---|
| Installation Failure | Update fails to install completely. | High | Corrupted download, insufficient disk space, incorrect permissions. |
| Update Conflict | New update conflicts with existing software. | Medium | Incompatible dependencies, outdated drivers, conflicting file versions. |
| Application Crash | Application crashes after update. | Medium | Incompatible libraries, corrupted files, missing or outdated system components. |
| System Instability | System becomes unstable or unresponsive after update. | Medium | Incompatible drivers, corrupted system files, insufficient system resources. |
Troubleshooting Techniques
Addressing software update problems often requires a systematic approach. This section details effective troubleshooting steps, file verification methods, version restoration strategies, conflict resolution procedures, and common error causes. A methodical approach is crucial for resolving these issues efficiently.A structured troubleshooting process is essential to identify the root cause of update problems. This often involves isolating the specific issue and applying targeted solutions.
By following a predefined sequence of checks, users can effectively diagnose and resolve software update problems.
Systematic Troubleshooting Steps
A systematic approach to troubleshooting software update problems is vital. This involves a series of checks designed to isolate the issue and apply targeted solutions. Below are some common steps:
- Verify system requirements: Ensure that the system meets the minimum specifications required for the software update. Insufficient resources (e.g., RAM, disk space) can lead to update failures.
- Check for network connectivity: A stable internet connection is essential for downloading and installing updates. Interruptions or slow connections can cause incomplete updates.
- Restart the system: A simple restart can resolve temporary glitches or conflicts that might prevent the update from completing.
- Check for pending updates: There might be other updates pending that could conflict with the current update process. Ensure that no other update installations are in progress.
- Run the update installer again: If the update process encounters an error, running the installer again might resolve it. Ensure that the correct installation path is accessible and there are no write restrictions.
Verifying Update File Integrity, Software update problems
Validating the integrity of downloaded update files is critical to ensure that the software is not corrupted. This process helps to prevent installation problems stemming from damaged or incomplete files.
- Using checksums: Checksums are unique hashes calculated from the file content. These hashes are used to verify that the downloaded file matches the original file. Comparing the calculated checksum with the expected checksum from the official source ensures the integrity of the downloaded update files. Tools like `md5sum` or `sha256sum` are used for checksum verification.
- Comparing file sizes: The downloaded file should match the expected size from the official update website. Significant discrepancies indicate potential corruption or incomplete downloads.
Restoring a Previous Software Version
If the update causes problems, reverting to a previous software version can be a solution. This method is crucial in safeguarding against severe issues caused by the update.
- Backup files: Before attempting any restoration, back up critical data to prevent data loss. This precaution is essential to safeguard against unintended consequences.
- Using backup tools: Software backup tools often include options for restoring to a previous state. Utilize these tools to safely revert to a working software version.
- Consult the documentation: Consult the software’s documentation for specific instructions on restoring a previous version. This is crucial for ensuring the process is executed correctly.
Resolving Software Conflicts
Software conflicts can arise when multiple programs require similar system resources. This can lead to update problems.
- Identifying conflicting software: Identify programs that might conflict with the software being updated. This might involve examining resource usage, especially during update installation.
- Updating conflicting software: Updating conflicting software to the latest compatible versions can often resolve the conflicts. This approach aims to align software components to the current system configuration.
- Checking for outdated drivers: Outdated drivers can also cause conflicts. Ensuring all drivers are up-to-date helps avoid these conflicts.
Common Update Errors and Resolutions
Several common update errors can occur. Understanding these issues and their resolutions can streamline the troubleshooting process.
- Error code 0x80070005: This error often signifies insufficient disk space or permissions issues. Resolving this error may involve freeing up disk space or adjusting file permissions.
- Error code 0x8007000B: This error indicates a problem with the update files. Re-downloading the update files or verifying their integrity may solve the issue.
System Requirements and Compatibility
Proper verification of system requirements is crucial before initiating any software update. Failing to do so can lead to unforeseen issues, ranging from corrupted data to complete system failure. Understanding the compatibility between software and hardware is paramount for a smooth and successful update process.System compatibility is influenced by various factors, including the operating system version, processor architecture, and available RAM.
These factors directly impact the software’s ability to function optimally. Different software versions often have varying minimum requirements, affecting the compatibility with older hardware configurations.
Importance of Verifying System Requirements
Thorough verification of system requirements before updating software is vital to prevent potential compatibility problems. This proactive step can save significant time and resources that might otherwise be spent troubleshooting issues arising from an incompatible system.
Factors Affecting Compatibility
Several factors influence the compatibility between software and hardware. Operating system versions play a significant role, as newer versions often introduce changes that older software might not be designed to handle. Processor architecture, including the specific instruction set, impacts the software’s ability to execute instructions efficiently. The amount of RAM available directly affects the software’s performance, especially when dealing with complex operations or large datasets.
Furthermore, the graphics card, if relevant to the software, also influences its functionality and compatibility.
Potential Compatibility Issues
Potential compatibility issues arising from software updates can manifest in various ways. For example, the software might fail to launch, display unexpected errors, or exhibit erratic behavior. A specific update might introduce new functionalities that older hardware components struggle to support. Another possibility is the update conflicting with existing applications, causing system instability or application crashes. In rare cases, incompatibility can lead to data loss or corruption.
Comparison of System Requirements Across Software Versions
Different versions of software often have varying system requirements. This difference is crucial to consider, as older versions might operate efficiently on older hardware but may not perform optimally on newer configurations. Conversely, newer versions may demand more powerful hardware, potentially rendering older systems incompatible. This disparity in requirements necessitates careful consideration when choosing which version of the software to deploy.
Compatibility Checks for a Specific Software Application
The following table Artikels the compatibility checks for a particular software application across different versions. This example highlights the need for consistent compatibility checks across various software releases.
| Software Version | Operating System | Processor | RAM |
|---|---|---|---|
| Version 1.0 | Windows 10 | Intel i5 | 8GB |
| Version 2.0 | Windows 11 | Intel i7 | 16GB |
User Interface and Error Messages
Understanding the structure and content of error messages is crucial for efficiently troubleshooting software update issues. These messages often contain valuable information that can pinpoint the cause of a problem. A well-designed user interface during updates can significantly improve the user experience, making the process smoother and less frustrating.Interpreting error messages and identifying patterns in their structure can significantly reduce the time spent resolving issues.
A clear and consistent user interface for software updates, coupled with informative error messages, enables users to quickly grasp the nature of the problem and take appropriate action.
Error Message Structure and Interpretation
Error messages often follow a structured format. This structure typically includes a descriptive error code, a brief explanation of the problem, and sometimes, suggestions for resolution. Recognizing these elements within the message allows users to pinpoint the source of the issue more quickly. For example, a message might display “Error Code: 1234 – Failed to download update file.
Please check your internet connection.” This provides a clear indication of the problem and the necessary action to resolve it.
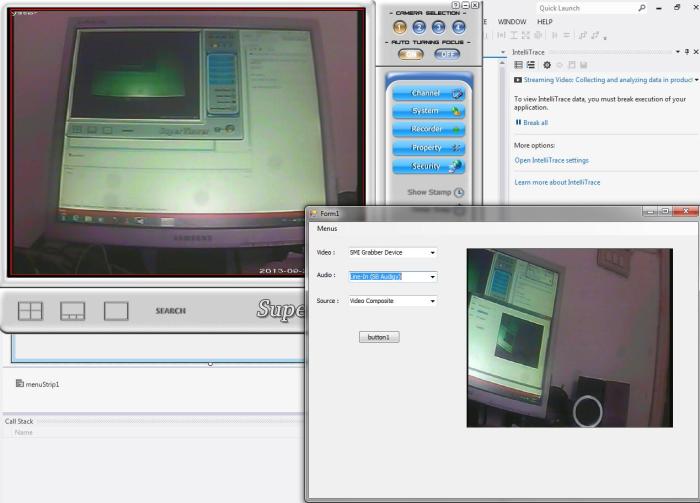
Common User Interface Elements During Updates
During software updates, common interface elements include progress bars, status indicators (e.g., downloading, installing), and informative labels or text. These visual cues provide users with real-time feedback on the update’s progress and status. The design of these elements plays a significant role in maintaining user engagement and reducing anxiety during the update process. For example, a visually appealing progress bar with clear descriptions can help users stay informed and patient.
Improving User Experience During Updates
To enhance the user experience, clear and concise language in error messages is essential. Avoid technical jargon or overly complex phrasing. Messages should be easily understandable, even for users unfamiliar with the software’s technical intricacies. Providing context-sensitive help or links to additional information can also prove beneficial. Including estimated completion times can also improve user perception of the update process.
Identifying Error Codes Within the Update Process
Error codes are numerical or alphanumeric identifiers that provide specific information about the nature of the update failure. These codes often correlate to specific issues, allowing for targeted troubleshooting. A comprehensive list of error codes and their corresponding explanations is a vital resource. For example, error code 500 might indicate a server-side issue. By understanding these codes, users can more effectively pinpoint the root cause of update problems.
Organizing Error Messages into Categories for Analysis
Categorizing error messages facilitates efficient troubleshooting. Grouping similar errors together helps identify recurring patterns or potential systemic issues. Categories can be based on the type of error (e.g., download errors, installation errors), the software module affected, or the user’s operating system. Creating a spreadsheet or a database to track and categorize these messages can help in long-term analysis.
For instance, a category for “Network Connectivity Issues” could group error messages related to internet problems during the update.
Software update problems are a persistent headache for many users, especially as technologies like technologies that will shape the future become more complex and integrated into our daily lives. These intricate systems require more robust update mechanisms to avoid compatibility issues and ensure seamless transitions. Ultimately, addressing these issues is crucial for a positive user experience.
Software Vendor Support
Effective communication and appropriate documentation are key when seeking assistance from software vendors regarding update problems. Understanding the various support channels and procedures can streamline the process and lead to a quicker resolution. This section details strategies for navigating vendor support effectively.Software vendors offer a range of support channels to address user concerns. Knowing which channel best suits your specific issue can expedite the resolution process.
Different Channels for Reaching Software Vendors
Various avenues exist for contacting software vendors, each with its own advantages and disadvantages. This variety caters to different needs and preferences.
- Online Support Forums/Communities: Many vendors maintain online forums or communities where users can post questions and seek assistance from other users or vendor representatives. These forums are often a good starting point for common issues, allowing you to leverage the collective knowledge of the community.
- Dedicated Support Websites: Vendor websites typically have a dedicated support section with FAQs, knowledge bases, and often troubleshooting guides. These resources can be invaluable in identifying potential solutions before contacting support staff.
- Phone Support: Phone support offers a more direct interaction with a vendor representative, allowing for immediate clarification and problem resolution, especially beneficial for complex or nuanced issues. However, it might not be the fastest option, especially if a large number of users are experiencing similar problems.
- Email Support: Email support provides a written record of your inquiry and resolution, which can be crucial for tracking progress and future reference. It often allows for a more detailed explanation of the issue, but response times may vary depending on the vendor’s workload.
Effective Communication with Vendors
Crafting clear and concise communication is essential for obtaining efficient support. A well-structured support request increases the likelihood of a timely and effective resolution.
- Detailed Description of the Problem: Clearly and concisely articulate the issue you are facing. Include specific error messages, steps to reproduce the problem, and any relevant system information. Avoid vague descriptions and focus on the observable actions that lead to the issue.
- Precise System Information: Provide the software version, operating system, and any relevant hardware details. This information helps the vendor understand the environment in which the issue arises and prevents unnecessary troubleshooting steps.
- Reproducible Steps: Include a detailed sequence of steps that consistently reproduce the problem. This allows the vendor to precisely replicate the issue and efficiently diagnose the root cause.
- Clear and Concise Language: Use precise and professional language. Avoid jargon or technical terms that the vendor might not understand. Maintain a polite and respectful tone.
Common Support Procedures and Policies
Vendors typically have established support procedures and policies. Understanding these guidelines can help you navigate the support process efficiently.
- Escalation Process: Most vendors have an escalation process for complex or unresolved issues. Understanding this process can help you effectively pursue resolution if initial support efforts are unsuccessful.
- Service Level Agreements (SLAs): Some vendors provide SLAs, which define the expected response times for different support requests. Familiarizing yourself with the SLA can help manage expectations.
- Software Updates and Support: Vendors often provide specific support for updates, sometimes with different support policies or response times compared to standard issues.
Documenting Software Update Issues
Thorough documentation is crucial for tracking and resolving software update problems. Maintaining a record of your communication with the vendor can be essential for future reference.
- Date and Time of Issue: Record the date and time when the issue first arose. This helps track the duration of the problem.
- Steps Taken to Reproduce the Problem: Maintain a detailed log of the steps you have taken to reproduce the issue.
- Support Ticket Number (if applicable): Note any assigned support ticket number to track the progress of your issue.
- All Communication with Vendor: Maintain a record of all emails, phone calls, or other communications with the vendor, including the date, time, and key points discussed.
Examples of Effective Support Requests
These examples demonstrate effective communication strategies when contacting vendors about update issues.
- Example 1: “Subject: Application X Update – Error
404. Version: 2.
5. OS: Windows 11 Pro. Steps to Reproduce:
1.Open Application X.
2. Click File > Open.
3. Select file.Error message: 404 – File Not Found. I’ve attached the file log.” (This example highlights clear subject, version, OS, and detailed steps to reproduce.)
- Example 2: “Subject: Software Y Update – Functionality Loss. Version: 1.0.
3. OS: macOS Monterey. Issue: After updating to version 1.0.3, the feature ‘Import Data’ stopped working.Steps to reproduce:
1. Click File > Import Data. Error message: (none). The feature previously worked without issues.” (This example shows a clear issue and detailed steps, highlighting the absence of an error message.)
Preventive Measures
Software updates, while crucial for maintaining system stability and security, can sometimes lead to unexpected problems. Proactive measures can significantly reduce the likelihood of encountering update-related issues. Careful planning and preparation are key to ensuring a smooth update process and a stable post-update environment.A well-defined strategy for software updates, encompassing preventive measures, can minimize disruptions and maintain system performance.
This approach includes steps for backing up data, identifying potential conflicts, and maintaining a stable software ecosystem.
Software update problems are a real pain, especially when they coincide with fluctuating market conditions, like the recent Bitcoin price volatility. Bitcoin price swings can impact developer focus, leading to delayed or rushed updates, which often exacerbates the initial problems. This can all lead to a frustrating user experience.
Data Backup Procedures
Proper data backup is paramount before any software update. A comprehensive backup strategy minimizes the risk of data loss during or after an update. This involves regularly backing up critical files and system data to an external drive, cloud storage, or other secure locations.
- Regularly schedule backups of critical data and system files to a secondary storage device.
- Employ cloud-based backup solutions for additional redundancy and accessibility.
- Verify the integrity of the backup by restoring a subset of data to ensure the backup process is effective.
- Establish a clear backup and restore protocol to minimize recovery time if necessary.
System Stability Assessment
Before initiating an update, assess the system’s stability to predict potential conflicts. This includes evaluating system resources (RAM, CPU, disk space), checking for outdated or incompatible software, and ensuring sufficient system stability for the update process.
- Review system resource usage to identify potential bottlenecks that might hinder the update process.
- Verify the compatibility of all installed software with the upcoming update version.
- Identify and resolve any known software conflicts or dependencies before the update.
- Ensure sufficient system resources, such as RAM and disk space, are available for the update process to avoid issues.
Conflict Resolution Strategies
Identifying and resolving potential update conflicts is essential. This involves examining software dependencies, verifying compatibility information, and using conflict resolution tools where available.
- Use system information tools to identify any conflicts between existing software and the update.
- Review the software update documentation to understand potential conflicts or dependencies.
- Utilize software conflict resolution tools if available to identify and address incompatibility issues.
- Thoroughly test the update process on a non-production environment to validate its impact and identify potential issues before applying it to the live system.
Maintaining a Stable Ecosystem
Maintaining a stable software ecosystem involves regular software updates and proactive system maintenance. This includes regularly updating drivers, security patches, and other critical software components.
- Keep all software components, including operating system, applications, and drivers, up-to-date.
- Implement regular system maintenance tasks, such as disk cleanup and defragmentation, to optimize system performance.
- Ensure that security patches are applied promptly to mitigate vulnerabilities that could affect the software ecosystem.
- Employ system monitoring tools to proactively identify and address potential performance or stability issues.
Update Logs and History
Update logs and history are invaluable resources for troubleshooting software issues. They record every significant change made to the software during an update, including modifications to files, configurations, and functionalities. Maintaining a comprehensive update log enables a more efficient and targeted approach to problem resolution.
Importance of Update Logs
Comprehensive update logs provide a historical record of modifications. This record is crucial for understanding the impact of each update and quickly identifying potential sources of problems. They offer valuable context for troubleshooting, allowing users to trace the introduction of bugs or regressions to specific update iterations.
Organizing and Reviewing Update Logs
Update logs are often structured in chronological order, listing the changes made in a particular update. To effectively review them, consider categorizing log entries by type (e.g., file modifications, configuration changes, feature additions). This organization makes it easier to quickly identify relevant entries related to a specific issue.
Extracting Relevant Information
Effective extraction of pertinent information from update logs requires a clear understanding of the problem. Carefully analyze the log entries related to the affected components or functionalities. This may involve searching for s associated with the problem, such as error messages, file names, or specific functions. Regular expressions or dedicated log parsing tools can help automate this process.
Interpreting Update Log Entries
Understanding the format and content of update log entries is essential. Each entry typically includes details such as the date and time of the change, the specific file or configuration modified, and a brief description of the modification. Careful review of these details allows for a more precise understanding of the impact of each update.
Using Update Logs to Diagnose Problems
Update logs provide a roadmap for diagnosing issues. By correlating log entries with observed symptoms, users can pinpoint the specific update or changes that introduced the problem. For example, if a new feature introduced in update 1.5 is causing a crash, the log entries associated with that update can help determine the exact cause of the crash. This method enables the isolation of the faulty component or change.
Impact of Updates on Existing Data: Software Update Problems

Software updates, while crucial for maintaining functionality and security, can potentially affect existing data. Understanding these potential impacts and implementing appropriate mitigation strategies is vital to preventing data loss and ensuring a smooth update process. Careful planning and execution are key to minimizing disruption and maintaining data integrity.
Potential Impacts of Updates on Existing Data
Updates can introduce compatibility issues with older data formats, leading to data corruption or loss. This is especially true for legacy systems or data structures not designed for the new update’s standards. In some cases, updates may unintentionally modify or delete existing data files, causing significant loss of information. Changes to the underlying database structure or file systems can also corrupt or render existing data inaccessible.
Mitigation Strategies for Data Loss During Updates
A proactive approach to data protection is essential. Regular backups are crucial. These backups should be stored securely in a separate location to safeguard against simultaneous failure of the primary system and the backup. This ensures a recovery point in case of unforeseen data loss. Testing the backup restoration process is critical to ensure its efficacy.
Strategies for Ensuring Data Integrity During Software Updates
Data integrity during updates hinges on a robust update process. Prior to implementation, thoroughly test the update on a non-production environment, such as a staging or development server. This testing phase allows for identification and resolution of any potential data issues before deploying to the main system. A phased rollout, starting with a small subset of users or systems, is another effective approach.
This allows for monitoring and feedback collection before the update is widely deployed. Comprehensive documentation of the update process, including specific changes and their potential impact on data, is vital.
Examples of How Data Can Be Affected by Updates
A common example is upgrading a database management system. If the new version uses a different data format or has stricter validation rules, existing data that doesn’t conform to the new standards may be rejected or corrupted during the update. Another scenario is an update to a file format used by the software. The update may not support the old format, leading to file incompatibility and data loss.
Similarly, an update that restructures an internal data table or alters the way data is stored can cause data inconsistencies or errors if the existing data isn’t compatible.
Methods for Recovering Data After Update Issues
If data loss occurs during an update, recovery strategies should be readily available. Restoring from a recent backup is the primary method. The backup must be validated to ensure its integrity before restoration. Alternatively, if the data loss is limited to specific files or records, a data recovery specialist may be necessary. If the update process involved database changes, the vendor may provide specific recovery procedures or tools to repair or restore data integrity.
Security Considerations During Updates
Software updates, while crucial for maintaining functionality and security, introduce inherent risks if not handled carefully. Improper update procedures can leave systems vulnerable to exploitation by malicious actors. Understanding these risks and implementing robust security measures is paramount for maintaining a secure environment.
Security Risks Associated with Updates
Software updates, while intended to enhance security, can sometimes introduce vulnerabilities if not thoroughly vetted. This can stem from incomplete testing, flawed code within the update itself, or unintended side effects from the update altering existing system configurations. Furthermore, the update process itself can be susceptible to attacks, either during the download or installation phases. This can allow attackers to inject malicious code or disrupt the update process.
A common concern is the potential for outdated or compromised update servers being exploited by attackers to distribute malicious software disguised as legitimate updates.
Measures to Ensure Security of the Update Process
Ensuring the security of the update process requires a multi-layered approach. Verifying the authenticity of the update source is critical. Employing digital signatures from trusted sources, and employing checksums or hashes for integrity checks, are essential steps. Furthermore, restricting access to update servers and implementing robust access controls for download and installation are important measures to minimize the risk of unauthorized access.
Examples of Malicious Software Exploiting Updates
Malicious actors can use various methods to exploit updates. One common method involves creating malicious software disguised as legitimate updates. Sophisticated attacks might manipulate update servers, altering legitimate update files with malicious code. Another example is employing zero-day exploits, which target vulnerabilities in the update process itself, to gain unauthorized access before patches are released. These attacks often rely on social engineering tactics, convincing users to install corrupted updates.
For instance, a user might be tricked into downloading a fake update from a seemingly legitimate website.
Strategies for Mitigating Security Risks During Updates
Several strategies can be employed to mitigate the security risks during updates. Regularly updating anti-virus software and employing intrusion detection systems can identify and prevent malicious code injection during the update process. Furthermore, rigorous testing and validation of updates are critical to minimize potential vulnerabilities. Creating and implementing an update management policy can help define processes for verification and approval, ensuring security best practices are followed.
Best Practices for Maintaining System Security During Updates
Maintaining system security during updates necessitates a proactive approach. Regularly backing up critical data is crucial, as updates can sometimes corrupt or overwrite data if errors occur. Employing a staged update approach, where updates are tested on a non-production environment first, can minimize the risk of impacting critical systems. Moreover, educating users about security risks associated with updates is vital for minimizing the risk of social engineering attacks.
This education should include warnings about suspicious updates and the importance of verifying the source.
Epilogue
In conclusion, navigating software update problems requires a multi-faceted approach. By understanding the potential issues, employing effective troubleshooting techniques, and utilizing vendor support, users can successfully manage updates and maintain a stable system. Prevention and proactive measures, such as data backups and thorough system checks, are also essential for a seamless upgrade experience.
Expert Answers
What are the common causes of update conflicts?
Update conflicts often arise from incompatible dependencies, outdated drivers, or corrupted files. It’s crucial to ensure all necessary components are up-to-date and functioning correctly before initiating an update.
How can I verify the integrity of update files?
Various methods exist to verify update integrity. Check the checksums against official sources or use dedicated software tools designed for this purpose.
What are the potential impacts of updates on existing data?
Updates can sometimes lead to data loss or corruption. Always back up your data before proceeding with any significant update to mitigate potential issues.
How do I effectively communicate update problems to software vendors?
Clearly document the problem, including error messages, steps to reproduce, and relevant system information. Provide as much detail as possible to help vendors diagnose the issue quickly.





